Overview
Identity and Access Management – Unbeatable Security
 As far as business operations are concerned, security is one among the most challenging tasks to be administered. Securing the right information at the right hands has always been a challenge. Safeguarding the resources, functionality, data and documents require a well-built safety system backed up by a strong security architecture.
As far as business operations are concerned, security is one among the most challenging tasks to be administered. Securing the right information at the right hands has always been a challenge. Safeguarding the resources, functionality, data and documents require a well-built safety system backed up by a strong security architecture.
Manage Identities
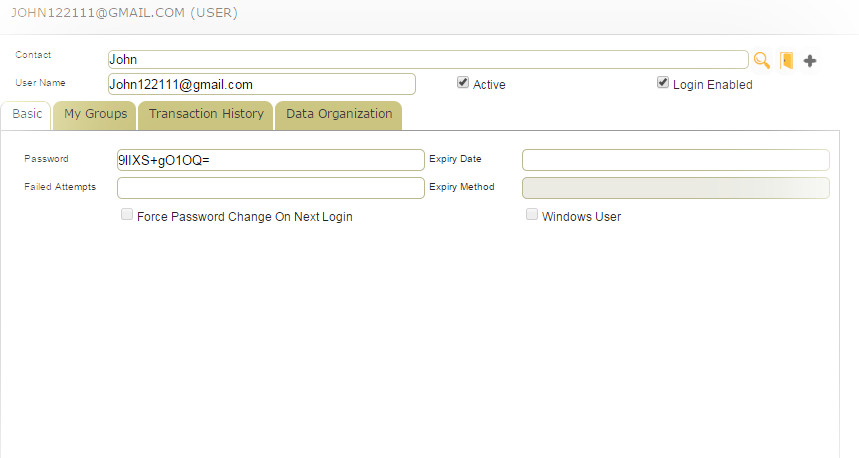
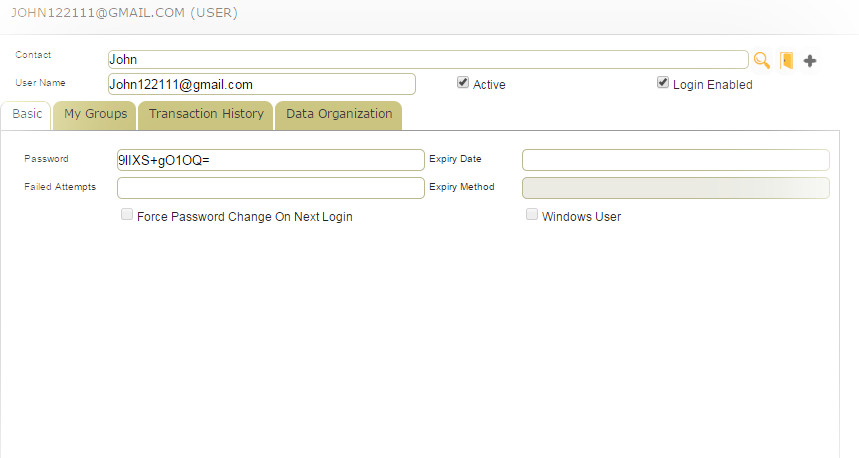
Secure First manages users and groups of all Biz First Apps through a centralized system. The users and groups can be custom assigned to Resources or Groups of Resources such as functions, data or documents.
Secure First manages users and groups of all Biz First Apps through a centralized system. The users and groups can be custom assigned to Resources or Groups of Resources such as functions, data or documents.
Manage Access
Every user component you see on BizFirst applications can be individually secured. Process, Rule, Service and Data components can be secured in this way. App and App Modules can also be secured. All Biz First Apps are protected by an additional layer of security provided by Secure First.
Every user component you see on BizFirst applications can be individually secured. Process, Rule, Service and Data components can be secured in this way. App and App Modules can also be secured. All Biz First Apps are protected by an additional layer of security provided by Secure First.
Data Level Security
BizFirst security protects the data objects such as dataconnection or datasource based on the data security. It also supports record-level security. Say for example, you can secure a particular doctor, book or file from one or multiple users or groups.
BizFirst security protects the data objects such as dataconnection or datasource based on the data security. It also supports record-level security. Say for example, you can secure a particular doctor, book or file from one or multiple users or groups.
Data Bucketing
Biz First introduced an innovative bucketing model too to ensure advanced level data security. This revolutionary model can provide you with a specialized logical data partitioning and protection algorithm. It also helps when you are creating zones (overlapping) or do segmentation across your entire database and arrange custom mapping for each user. Even though the theory seems a bit complex to understand, on implementing it, you will realize that it opens up a great potential to build a highly secured system.
Biz First introduced an innovative bucketing model too to ensure advanced level data security. This revolutionary model can provide you with a specialized logical data partitioning and protection algorithm. It also helps when you are creating zones (overlapping) or do segmentation across your entire database and arrange custom mapping for each user. Even though the theory seems a bit complex to understand, on implementing it, you will realize that it opens up a great potential to build a highly secured system.
Features

IdentityManagement
You can simply define all the users and user groups once and can use it everywhere. More Details...
AccessManagement
Secure First Access Management System validates each user against each resource it tries to access. More Details...
SecurityModels
Secure First puts forth three distinct security models – a Security Architect can decide over which model is best suited for their subsystem during the product-planning phase. More Details...
DataZoning
There are many prevailing access management systems in the market, which do a fair job in organizing identities (users) and also up to a certain extent in handling the access control (mapping between identity and target resource). More Details...
